What Just Happened? The Case of The Accidental Multi-Cloud.
In spite of our best intentions to operate within given standards, employees will naturally seek out the best tools to fulfill the tasks they are expected to complete. This means that people may naturally gravitate toward previously unapproved solutions that may make it easier for them to complete their work. If their choice of tools span multiple providers and cloud environments this can create an accidental multi-cloud implementation. Done correctly, multi-cloud can lead to increased productivity and innovation. Without governance, accidental multi-cloud environments can create additional management overhead, security risk, billing confusion, and vendor sprawl.
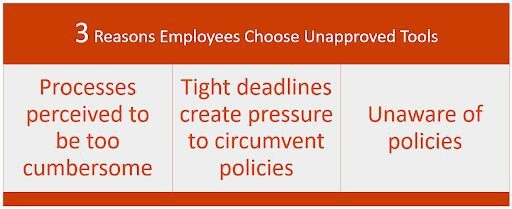
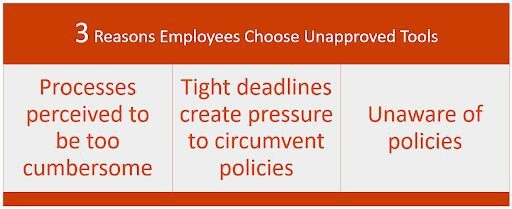
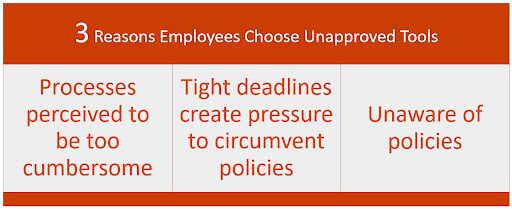
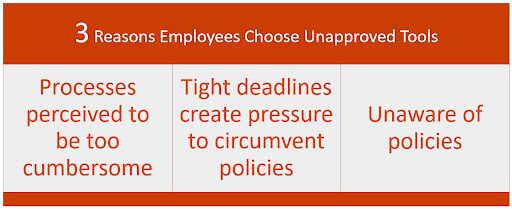
When users adopt unapproved cloud apps and services, our goal is to bring these solutions into our standardized processes while still enabling teams to choose the right tool for the job; wherever it may live. The top three reasons users adopt unapproved applications and services are:
- Current processes and procedures are too cumbersome to be followed for what is believed to be an inconsequential change. Your users willfully circumvent policy to meet the needs of an individual or group of clients.
- The timelines required to complete a project are too tight and intense to follow normal processes. In this instance, the policy is also willfully circumvented due to the needs of the business.
- The individual or group of clients are unaware of the policies and processes that they are expected to follow. This may stem purely from an educational issue, but may also expose problems with how you are communicating your documented policies across departments.
These decisions at a micro level can certainly cause some macro-level concerns that require many working hours to remediate. That remediation time sidelines existing projects, causing unintended delays and expense to outstanding projects that are well vetted, budgeted, and currently in your queue. Most, if not all of us have been involved in similar situations. But, what do we call this type of action and how can this ultimately force us into unintended circumstances of having to deal with potentially new platforms or environments with which we weren’t particularly prepared to immediately mesh?
The Intersection of Shadow IT and Public Clouds
All of the scenarios described above fit into the term “Shadow IT.” For those that may be unaware, “Shadow IT” is a phrase used to describe software and services that are deployed outside the purview of your dedicated IT organization. Unauthorized services and software can be cause for major alarm within your organization, as they are not managed under the umbrella of any processes, procedures, security standards, or strategies that your teams have put large amounts of effort into fleshing out and enforcing.
Although I’ve spoken and written many times about how important a cloud strategy is for the success of your go-to-cloud model, Shadow IT can create a situation very different from what you planned. If any services or software have been deployed into a hyperscale cloud (AWS, GCP, Azure) without the knowledge of your IT org, you will need to rapidly find a way to bring these into compliance without the benefit of strategizing ahead of time. Business users, developers, and other teams may start using cloud-based solutions that need to be folded into your architecture quickly, without much forethought or strategic planning for how they fit into your existing architecture.
How Shadow IT Increases Cloud Adoption
This type of situation can be triggered by almost anyone in your company regardless of their technical mastery or their understanding of your current compliance and strategic initiatives. However, it is safe to say that it would most commonly be expected from members of your technical teams.
Some of the more granular examples that can lead to Shadow IT leading the charge on cloud adoption:
- A software solution was deployed as a Proof of Concept into a Private Cloud provider and large effort was spent on configuring the product for use and stability. This is a very real possibility with products that ingest and make sense of numbers, such as Finance or Accounting groups.
- “Get It Done” mentality. Code that was built in a Private Cloud without portability in mind to suit a business need and without regard to your existing platforms. Sometimes the “get it done” mentality leads to split-second decisions that can be quite cumbersome to refactor without a major uptick in cost.
- A subscribed/licensed purchase “under the gun” to take advantage of discounts or specials. Getting more use for less investment can also lead to rapid-fire decisions that can lead to purchasing before planning.
- Pet projects that were never meant to go to production and are quite fragile, but become an obvious boon to your current solutions. Sometimes we start off with the best intentions and end up down a creek without a strategy.
- You realize that there is a tool that is much more simple or cost-efficient within a private cloud solution that is immediately needed to complete an in-flight project with imminent deadlines. The sprawl of options and capabilities within Cloud providers means that you may suddenly find a bread crumb of information that leads to an unexpected solution. In some scenarios, this may need to be acted on quickly.
- Your DBAs have unknowingly reached critical mass and you need to move them to a more scalable solution immediately.
It’s clear that almost anyone in the organization can be an agent of change when they not only want but immediately require one or more cloud solutions, without the appropriate time to plan prior to adoption and integration. When multiple teams select solutions from different cloud providers, your organization may find itself in a de facto multi-cloud environment.
Catalyst for Change: COVID-19 + Remote Workers
To drive home the criticality of bringing these services and software back under IT control, most cloud providers and SaaS solutions have seen a massive uptick in adoption in 2020 due to COVID-19. The majority of the workforce has transitioned to working from home full time. There has been a 50% increase in enterprise cloud usage across all industries. For example, Manufacturing alone has increased 144%, Financial Services rose 36% and enterprise cloud usage from non-IT-managed devices has doubled. Interestingly, but not too surprisingly, both Manufacturing and Financial Services are two of the most “at-risk to security breach” industries in 2020. These statistics should help demonstrate the urgency of identifying Shadow IT operations and pulling them into the fold of compliance as soon as it’s discovered.
Whether this situation has been created by sources internal or external to your department, you now know about its existence and it’s time to take a deep breath and act decisively to protect your policies and the security of your environments.
Multi-Cloud: Happy Accidents


This is also an amazing chance, if possible, to review, modify, or even completely remodel any of your existing strategies to encompass Multi-Cloud. Organizations across industries are adopting multi-cloud because of the flexibility to use the best-of-breed services from each cloud. Your development team may use Google Cloud for dev/test workloads, your IT department might choose AWS for disaster recovery, and your data scientists might choose Azure to process business analytics data.
- Implement a company-wide IT asset management system that detects new services
- Listen to end users to take advantage of their role-specific knowledge to identify requirements for new services and help similar departments standardize on the best of the options
- Optimize your data storage solutions to avoid duplication of volumes and reduce egress charges.
While the actions of your Shadow IT departments may cause you some initial stress, remember that IT transformation only comes from change, and rapid transformation may have just been brought to you on a silver-lined platter.
With the right approach, IT can be a strong partner for your business users and developers by empowering them to safely and efficiently adopt cloud tools that help them be more productive. Accomplishing this role change requires making your company’s data available to your users via low-latency stores that are simultaneously available to on-prem and each of the desired public clouds.
Faction CCVs can accept your data and make it simultaneously available to any cloud you may need, minimizing management overhead and expensive fees. We can also accept your data via a great many ways, including the native replication methods of the array you may already own. Contact us for assistance in transforming your accidental multi-cloud into an asset.
Learn more about multi-cloud solutions here.
Nathan Mills is the Consulting Cloud Architect in the Managed Services team at Faction Inc. Nathan has performed in Cloud Architecture positions for both VMware on the vCloud Air product and at OVH US prior to Faction Inc. He holds a long history of solutions, support, and world-class service for these companies as well as Webroot (now Open Text) and Mile High Banks.